Decentralization
Decentralization refers to the shift of control and decision making from a central authority to a distributed network and can be visualized on a spectrum based on the priorities of the blockchain network. Decentralization has many applications, and crypto projects may have different motivations for leveraging a decentralized model including distributed decision-making, distribution of wealth, or security. Although it’s often considered the cornerstone of blockchain technology, not all crypto projects approach decentralization in the same way.
For example, if a network prioritizes the speed of transactions, they may compromise on security, meaning there are fewer nodes responsible for verifying the authenticity of transactions. The fewer number of nodes verifying transactions, the more responsibility or trust each individual node must take on which can lead to security vulnerabilities (and outages). Alternatively, by distributing trust across more nodes, networks can more effectively deter bad actors with intentions to harm the network. With workload spread out evenly across the network, verification of authenticity becomes a much more diligent process and the network in aggregate is less vulnerable.
Transparency
At its core, a blockchain is a public, immutable ledger on which transactions are recorded after appropriate verification by designated network participants known as nodes. This means all transactional activity/information is observable and accessible by anyone using the network and cannot be changed. In contrast, the flow of funds on ledgers of traditional financial institutions are gate-kept by those institutions themselves and are often not immutable.
Computational Logic
The functionality of a blockchain is heavily reliant on computational logic like algorithms and predefined rules that allow nodes to effectively interact with each other and make sure the correct funds make it from point A to point B. The computational logic will often vary based on the blockchain environment.
Enterprises use different algorithms and predefined rules than public blockchains to fulfill their particular use case and business needs. Depending on how sensitive the data is that’s being held on the blockchain, the enterprise might put stricter controls in place to manage who can send transactions and who can validate them. For instance, an airline using blockchain to crosscheck travel documents with flight data is handling much more sensitive information than a retailer using blockchain to track goods from source to end consumer, so more predefined permissions may be employed to ensure transactions are being validated by trustworthy people within the organization. It’s important to note that centralized organizations don’t rely as heavily on distributed trust as public blockchains like the Bitcoin and Ethereum network do
Trust
Blockchain technology seeks to minimize the amount of trust needed by a single entity to achieve consensus. Blockchains are often described as trustless but this isn’t entirely accurate. There are two current mechanisms for achieving consensus in a distributed network: proof of work and proof of stake. We’ll go into these further in a future post, but at a high level one is performed by solving complex mathematical problems while the other is performed by staking funds to a smart contract. Both are designed to incentivize participants to reach consensus in good faith using a combination of economics, game theory, and complex mathematics. Although fundamentally different, both methods help facilitate the distribution of trust within a blockchain environment.
Security
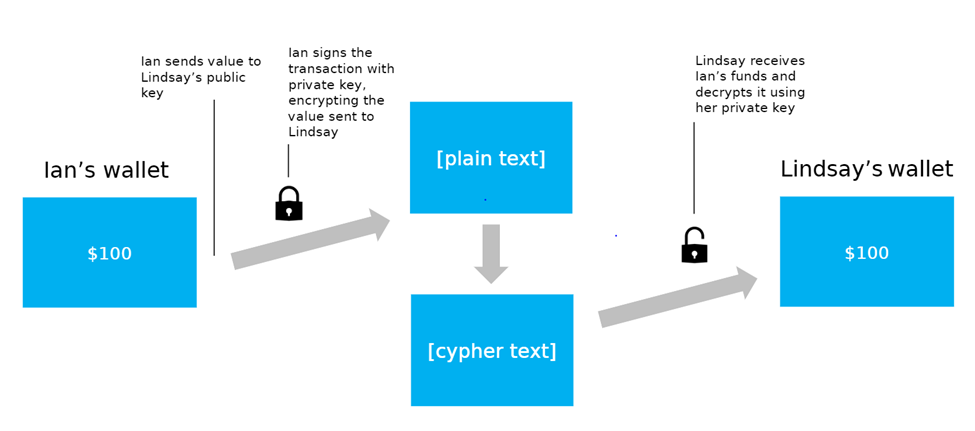
At the block level, peer-to-peer transactions are encrypted by asymmetrical cryptography, more commonly known as public-key cryptography. Public-key cryptography uses a set of public and private keys to confirm transactions are authentic and prevent them from being altered. While your public key is visible to anyone on the network, your private key is visible to only you. Here is public-key cryptography visualized in a peer-to-peer context:
Conclusion
The tenets behind blockchain technology are becoming increasingly dependent on each other as blockchain networks scale to onboard new users. In our next post, we’ll use this framework to explore and evaluate the two largest blockchain networks: Bitcoin and Ethereum.
The post appeared first on Bittrex.com - The Next Generation Crypto-Currency Exchange.